# create a new key pair
gpg --full-generate-key
# get the fingerprints
gpg --list-public-keys
# get the base64 public key. --armor specifies the output to be ASCII
gpg --armor --export F73BA78DEDEDC2FBDF293EC92D5B77BC9E4457F3
# decrypt a message
gpg --decrypt temp.txtScript to paste into windows that don’t allow pasting. This is useful for VMs that dont have access to the clipboard.
#!/bin/bash
# set X display
export DISPLAY=":0"
sleep 0.5 # fat-finger protection
# get the clipboard content and send it as keypresses
xdotool type -- "$(xclip -o -selection clipboard)"put it in nginx.conf
stream {
# load balance the ldap servers because why not.
upstream ldaps_servers {
server server1.local:636;
server server2.local:636;
}
server {
listen 127.0.0.1:389; # listen on regular unencrypted LDAP
proxy_pass ldaps_servers; # pass traffic to the LDAPS servers
proxy_ssl on; # encypt traffic sent to ldap servers
}
}server {
listen 80 default_server;
listen [::]:80 default_server;
#if ( $request_uri ~* "%0A|%0D" ) { return 403; }
rewrite ^(.*)(\r|%0D)(.*)$ $1$3 permanent;
rewrite ^(.*)(\s|%20)(.*)$ $1$3 permanent;
root /var/www/html;
# Add index.php to the list if you are using PHP
index index.html index.htm index.nginx-debian.html;
server_name _;
location / {
# First attempt to serve request as file, then
# as directory, then fall back to displaying a 404.
try_files $uri $uri/ =404;
# proxy_pass http://localhost:8080;
# proxy_http_version 1.1;
# proxy_set_header Upgrade $http_upgrade;
# proxy_set_header Connection 'upgrade';
# proxy_set_header Host $host;
# proxy_cache_bypass $http_upgrade;
}
}^ - Start of the string.(.*) - Captures any characters (the first part of the URI) and stores it in a capture group $1.(\r|%0D) - Looks for either a literal carriage return (\r) or its URL-encoded equivalent (%0D). This is the part we are trying to remove.(.*) - Captures the remaining part of the URI after the carriage return and stores it in capture group $3.$ - End of the string.$1$3 - This is the rewritten URL, which concatenates the first and third capture groups, effectively removing the carriage return (\r) or %0D.permanent - This specifies a permanent HTTP 301 redirect, which tells the browser that the redirect is permanent and the new URL should be used in future requests.threatlocker ringfence bypass for powershell network access
# this works if you can install an http proxy
iwr 'https://ipinfo.io' -Proxy 'http://10.0.0.1:8080'
# powershell 5 doesnt support socks5 but curl.exe does
ssh -N -D 8080 cwcraft@caleb-craft.com
curl.exe 'https://ipinfo.io' --proxy 'socks5://127.0.0.1:8080'
# pwsh.exe is not ringfenced
iwr 'https://ipinfo.io' -Proxy 'http://127.0.0.1:8080'
# pwsh.exe does support socsk5
iwr 'https://ipinfo.io' -Proxy 'socks5://127.0.0.1:8080'node.exe can be used as an alternative to curl or Invoke-WebRequest
This can bypass restrictions like ThreatLocker, but should probably raise a flag in EDR tools. I havent seen anything yet.
#set URL
$url = "https://ipinfo.io/ip"
# Alternate curl/Invoke-WebRequest
& "C:\Program Files\Adobe\Adobe Creative Cloud Experience\libs\node.exe" -e "`$http=require('https');`$http.get('$url', `$res => `$res.pipe(process.stdout));"places to look for node.exe:
C:\Program Files\Common Files\Adobe\Creative Cloud Libraries\libs\node.exeC:\Program Files\Adobe\Adobe Creative Cloud Experience\libs\node.exeType: ~.
Sending an escape character ~ followed by a dot . will close the connection. The escape character only works at the beginning of a line, so you my need to press “Enter” first.
# ssh tunnel to make accessible from internet
ssh -N -f -R 0.0.0.0:55555:localhost:22 user@example.org
# ^ ^internet port ^local port
# |
# Specify wildcard. default is localhost*
# *you may need to edit /etc/ssh/sshd.config to set:
# GatewayPorts=clientspecified
# upgraded to autossh to keep connection alive
autossh -N -f -R 127.0.0.2:55555:localhost:22 user@example.org
# ^
# |
# Use different localhost addresses to organize multiple connections if youre using the same port
# look for connections
netstat -nlp | grep 55555
# connecting to it
ssh -J user@example.org user@localhost -p 55555
-N - Do not execute a remote command.-f - Requests ssh to go to background just before command execution.-R - Specifies that connections to the given TCP port or Unix socket on the remote (server) host are to be forwarded to the local side.ssh -N -D 8080 user@example.org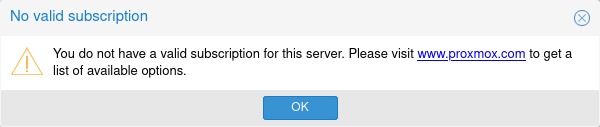
Edit the Javascript file:
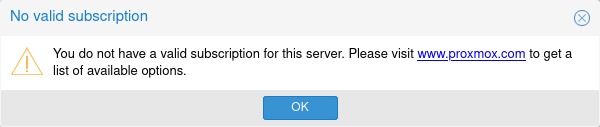
vim /usr/share/javascript/proxmox-widget-toolkit/proxmoxlib.jsFind the lines:
Ext.Msg.show({
title: gettext('No valid subscription'),Void the function:
void({ //Ext.Msg.show({
title: gettext('No valid subscription'),Restart the service:
systemctl restart pveproxy.service# view cert
openssl s_ check cert dates
# view expiration cert dates
openssl s_client -connect example.org:443 | openssl x509 -noout -datesecho '1' >> /proc/sys/net/ipv4/ip_forward# add iptables rules to route traffic from main interfaces to the vpn (i dont fully understand this)
iptables -t nat -A POSTROUTING -o tun+ -j MASQUERADE
iptables -A FORWARD -i ens+ -o tun+ -j ACCEPT
iptables -A FORWARD -o tun+ -j ACCEPT
iptables -A FORWARD -i tun+ -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -i tun+ -j ACCEPTclients dont need much. mainly, they just need a default route pointing to the entry server.
sudo ip route del default
sudo ip route add default via 10.0.0.173you might be better off just using DHCP.
about:config
browser.newtabpage.activity-stream.showSponsoredTopSites
false#pip3 install uploadserver
#apt install qrencode
qrencode "http://$(hostname -I | tr -d ' '):8000/upload" -o - | feh - &
python3 -m uploadserver# mount NFS share
sudo mount -t nfs <nfs_server:/path/to/share> /mnt
# mount windows partition that is hibernated
mount -t ntfs-3g -o remove_hiberfile /dev/<sdx0> /mnt:w !sudo tee %
:.w !bash
:set number
:set paste
change tty[1-6] to titty[1-6]
sudo sed -r -i 's/(ti)?\\l/ti\\l/g' /etc/issue# set X display
export DISPLAY=":0"
distance=10 # radius of the jiggle
delay=0.1 # time in seconds to wait between jiggles
while true
do
randomAngle=$((1 + RANDOM % 360))
inverseAngle=$(( ($randomAngle+180) % 360))
# move random direction
xdotool mousemove_relative --polar $randomAngle $distance
sleep $delay
# return to initial position
xdotool mousemove_relative --polar $inverseAngle $distance
sleep $delay
donetricks to run on peoples linux computers when they forget to lock them.
# increasingly slower bash startup
echo 'sleep 0.01' >> ~/.bashrc # or ~/.bash_profile